Discounts always applied to volume sales
Shadowsocks Proxy
Managed Shadowsocks servers on dedicated datacenter IPs. Your traffic passes inspections from any firewall. No shared servers, no bandwidth caps, no configuration headaches.
- AEAD Encryption
- DPI Bypass
- Dedicated Servers
- Works on any device
- Faster than a VPN
Shadowsocks Proxies Pricing
Shadowsocks Proxies pricing that scales with your operation. Volume discounts kick in automatically - the more IPs you need, the less you pay per IP. Longer billing periods drop the price further. Use the calculator below to find your exact cost before you commitWhat Is Shadowsocks?
A regular proxy is easy to block. Its traffic pattern is obvious -- a VPN handshake, a SOCKS5 connection, an HTTP CONNECT request. Deep packet inspection systems identify and drop these in milliseconds.
Shadowsocks was designed specifically for this problem. It uses AEAD symmetric encryption to make your traffic look like random noise to any inspection system. There is no protocol fingerprint to detect. No handshake to block. No VPN pattern to flag.
We run the server side. You run the client. Your traffic goes from your device to our datacenter server, encrypted end-to-end, and hits the open internet from there. Setup is a credential paste, not a week of configuration.
Shadowsocks is an open-source encrypted proxy protocol created in 2012. It was built to solve one specific problem: getting traffic through firewalls that inspect and block conventional proxy and VPN connections.
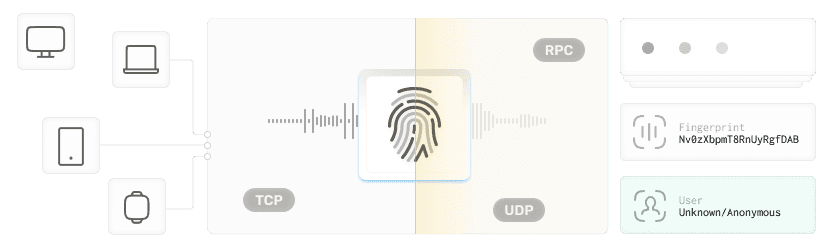
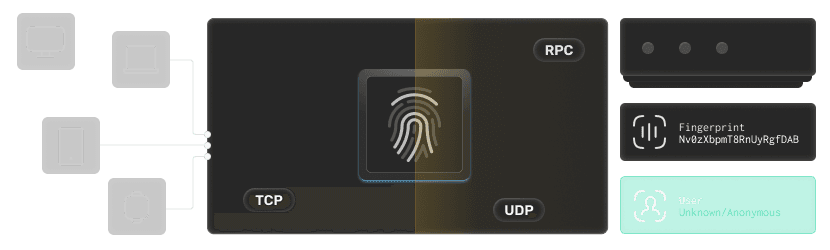
Unlike a VPN, Shadowsocks does not encrypt all traffic on your device. It creates a local SOCKS5 listener (ss-local) on your machine that applications connect to. That local endpoint encrypts your traffic and forwards it to a remote server (ss-remote) which you control. The remote server decrypts and forwards the request to the destination. Responses come back the same way in reverse.
The critical difference from a standard SOCKS5 proxy: the traffic between ss-local and ss-remote is encrypted with AEAD ciphers (ChaCha20-Poly1305 or AES-256-GCM). To any network observer or deep packet inspection system watching the connection, it looks like encrypted HTTPS traffic. There is no identifier that marks it as Shadowsocks.
The architecture in plain terms:
Your app -> ss-local (localhost) -> [AEAD encrypted tunnel] -> ss-remote (our server) -> target website
Traffic between your device and our server is encrypted. Traffic from our server to the destination is standard HTTPS/HTTP. Your IP at the destination is our server's IP.
Shadowsocks Use Cases
How Shadowsocks Bypasses Deep Packet Inspection
Most censorship and corporate firewalls work by identifying traffic patterns. A VPN connection has a recognizable TLS handshake and protocol negotiation sequence. A SOCKS5 connection starts with a specific byte sequence. HTTP proxies have CONNECT headers. All of these are trivial to detect and block.
Shadowsocks traffic looks different. The connection starts with a random-looking payload (because it is encrypted). There is no standard handshake pattern to fingerprint. The stream length, timing, and byte distribution resemble encrypted HTTPS rather than any known proxy protocol.
Three things make this work:
- AEAD encryption from byte one. The first byte of every Shadowsocks connection is already ciphertext. There is no unencrypted negotiation phase for a firewall to analyze.
- No fixed port requirement. Shadowsocks can run on any port, including 443 (HTTPS). Traffic on port 443 that looks like HTTPS is rarely blocked -- doing so would break the entire web.
- No protocol signature. Tools like Wireshark and commercial DPI appliances maintain signature databases for known proxy protocols. Shadowsocks has no stable signature to match.
This is why Shadowsocks remains one of the most effective censorship bypass tools more than a decade after it was created.
Shadowsocks vs SOCKS5 vs VPN vs Trojan -- Which One Do You Need?
Feature | Shadowsocks | SOCKS5 Proxy | VPN (WireGuard) | Trojan Proxy |
|---|---|---|---|---|
Traffic encryption | Yes - AEAD (ChaCha20, AES-256) | No | Yes - full tunnel | Yes - mimics HTTPS |
DPI bypass | Yes - random-looking ciphertext | No - detectable pattern | Depends on implementation | Yes - uses real TLS |
Speed vs VPN | Faster - proxy only, no full tunnel | Fastest | Slower - full tunnel overhead | Fast - TLS overhead only |
Detectable by ISP? | Very hard | Easily | Depends on protocol | Very hard |
Client required | Yes - Shadowsocks client app | Any SOCKS5-capable tool | VPN app or wireguard config | Trojan client |
Best for | Censorship bypass, obfuscated scraping | Speed-priority tasks, no encryption needed | Full privacy, IP masking | Censorship bypass, highest stealth |
Our product | This page |
Pick Shadowsocks if: Your primary need is bypassing firewalls or DPI-based blocking. You want encryption but not the overhead of a full VPN. You know how to configure a Shadowsocks client or are willing to spend 10 minutes on it.
Pick SOCKS5 if: You do not face active traffic inspection and you want maximum speed with no encryption overhead. See our dedicated SOCKS5 proxies.
Pick Amnezia VPN if: You need full IP masking, all-traffic encryption, and a simpler setup than Shadowsocks. See our Amnezia VPN.
Pick Trojan if: You need the highest possible stealth - Trojan impersonates actual HTTPS traffic with a valid TLS certificate, making it harder to detect even than Shadowsocks. See our Trojan proxy.
Datacenter Shadowsocks vs ISP Shadowsocks - Which One?
We offer Shadowsocks on two IP types. Here is when each makes sense:
Datacenter Shadowsocks (this page) | ISP Shadowsocks | |
|---|---|---|
IP source | Datacenter-hosted IPs | ISP-assigned residential IPs |
Speed | Higher -- pure datacenter infrastructure | Slightly lower -- routes through ISP infrastructure |
Detection by anti-bot | Flagged on sites with IP reputation checks | Passes as residential user |
Price | Lower | Higher |
Best for | Censorship bypass, firewall traversal, obfuscated scraping where IP trust is not critical | Platforms that block datacenter IPs even after Shadowsocks obfuscation |
If you just need to get through a firewall or bypass DPI, datacenter Shadowsocks is faster and cheaper.
If you are targeting sites that block datacenter IP ranges regardless of traffic obfuscation, our ISP Shadowsocks uses residential IPs that pass those checks.
Shadowsocks Client Compatibility
Our servers work with any standard Shadowsocks client. Here is what we recommend per platform:
Platform | Client | Notes |
|---|---|---|
Windows | Shadowsocks for Windows, Clash | Shadowsocks for Windows is the simplest; Clash for rule-based routing |
macOS | ShadowsocksX-NG, Clash for Mac | ShadowsocksX-NG is the go-to for quick setup |
iOS | Shadowrocket, Potatso | Shadowrocket is the most widely used paid option |
Android | Shadowsocks Android | Free, official, works on all Android versions |
Linux | shadowsocks-libev, Xray | shadowsocks-libev for servers; Xray for advanced configs |
Router | OpenWrt with shadowsocks-libev | Configure once, all devices on the network benefit |
Browser | Via SOCKS5 proxy settings | Once ss-local is running, point browser to localhost:1080 |
After purchase, you get: server IP, port, password, and cipher in your dashboard. Paste these four values into any client listed above.
Shadowsocks Frequently Asked Questions
Frequently Asked Questions
What is Shadowsocks and how is it different from a VPN?
Shadowsocks is an encrypted proxy protocol that creates a local SOCKS5 endpoint on your device, encrypts your traffic with AEAD ciphers, and routes it through a remote server. Unlike a VPN, it does not tunnel all your traffic -- only what you configure. It is lighter and faster than a VPN and harder to detect by deep packet inspection because the traffic looks like random HTTPS rather than a recognized VPN protocol.
Is Shadowsocks still working in countries with heavy censorship and network filtering?
Yes. Shadowsocks remains effective in heavily filtered networks when used with current AEAD ciphers (ChaCha20-Poly1305 or AES-256-GCM) on a clean server IP. The protocol has no detectable fingerprint for standard DPI systems. For the most restrictive environments, combining it with obfuscation plugins (simple-obfs, v2ray-plugin) adds additional disguise. We support Shadowsocks 2022 on request for improved replay protection.
What ciphers do your Shadowsocks servers use?
Our servers support ChaCha20-Poly1305. These are the current AEAD (Authenticated Encryption with Associated Data) standards. We do not support legacy stream ciphers like RC4 or AES-CFB -- they have known weaknesses and are increasingly detectable by modern inspection systems.
What Shadowsocks clients work with your servers?
Our servers work with any standard Shadowsocks client: Shadowsocks for Windows, ShadowsocksX-NG (macOS), Shadowsocks Android, Shadowrocket (iOS), shadowsocks-libev (Linux), and Clash on all platforms. After purchase, you get server IP, port, password, and cipher from your dashboard. Paste those four values into any client.
How is Shadowsocks different from a SOCKS5 proxy?
A SOCKS5 proxy forwards your traffic unencrypted. Any network observer, ISP, or firewall can see the connection is a proxy and block it. Shadowsocks encrypts the tunnel between your client and server with AEAD ciphers. The traffic is indistinguishable from regular HTTPS to any passive observer. SOCKS5 is faster when detection is not a concern. Shadowsocks is required when it is.
What is the difference between Datacenter Shadowsocks and ISP Shadowsocks?
Datacenter Shadowsocks uses IPs hosted in datacenter infrastructure. ISP Shadowsocks uses IPs assigned by real Internet Service Providers. Both use the same Shadowsocks protocol. The difference is IP reputation: some targets block datacenter IP ranges regardless of traffic obfuscation. ISP IPs pass those checks because they look like residential users. For censorship bypass and general DPI evasion, datacenter Shadowsocks is faster and cheaper. For targets that block datacenter ASNs, use our ISP Shadowsocks.
Do I need to configure anything on the server side?
No. We manage the server. You receive four values after purchase: server IP, port, password, and cipher name. Enter those in your Shadowsocks client. The server is already running and configured. If you need a specific port, cipher, or advanced configuration, contact support and we will set it up.
Shadowsocks Proxies Features
Full UDP/QUIC and TCP support
The only proxy type that handles both. Works with torrent clients, game engines, VoIP, DNS, and any other UDP application alongside all standard TCP/HTTP traffic.
20+ global locations
North America, Europe, and Asia-Pacific. Select location at checkout. All locations carry the same uptime SLA.
Dedicated IPs
Our IPs are not shared with other customers. What you buy is yours, not recycled from a shared pool.
Versatile
Shadowsocks supports a wide range of platforms such as Windows, Linux, Mac, Android, and iOS for seamless use across devices.
Secure
Shadowsocks excels in anonymity, hiding your IP and encrypting traffic to keep your personal data private.
Flexible Encryption
With a customizable encryption approach, Shadowsocks can be modified in any way that fits you the best.
Ultra-Fast
Using cutting-edge async I/O and event-driven tech with a simple SOCKS5 proxy, Shadowsocks offers next-gen speed and seamless connectivity.
Pick Your IP address
We don't sell you packages. You can pick each IP address individually by subnet, city, state or country. You're in full control.
Unlimited Bandwidth
We're not placing any sorts of limits on your bandwith so you can enjoy really fast and responsive proxies for your applications.
Dual Authentication
Don't want to use a username and password combo to authenticate to your proxies? No problem, you can use your ip address instead.
Shadowsocks Proxies Compatibility
Our Shadowsocks Proxies are compatible with a wide range of devices and platforms.Worldwide services
Millions of residential proxies across the globe and hundreds of datacenter locations. We're constantly expanding our network to bring you the best possible service.