Worldwide services
Millions of residential proxies across the globe and hundreds of datacenter locations. We're constantly expanding our network to bring you the best possible service.
Millions of residential proxies across the globe and hundreds of datacenter locations. We're constantly expanding our network to bring you the best possible service.
Discounts always applied to volume sales
Overcome even the strictest internet censorship in the world and experience uninterrupted surfing by using our Trojan proxies. These proxies are specially designed to go around all kinds of geo restrictions and network surveillance. Unlock any kind of otherwise inaccessible content by utilising this proxy protocol and enjoy an elevated browsing experience.
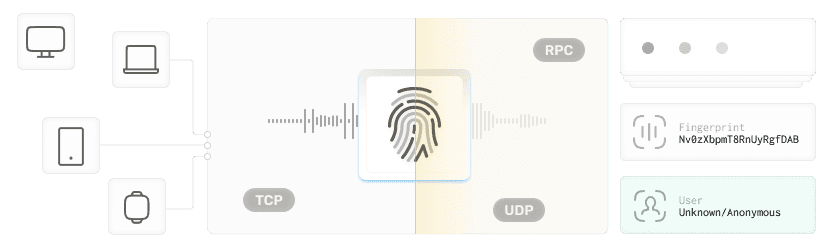
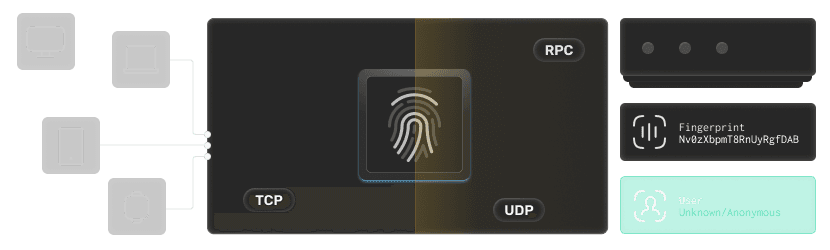
A Trojan Proxy is a kind of special proxy protocol that tunnels your internet data through port 443, which is the same port used by most encrypted, HTTPS websites. That makes your data look like normal HTTPS activity, so all firewalls and network monitoring tools see your activity as regular web traffic. Unlike other, more complicated encryption tools, Trojan proxies focus more in blending into current HTTPS streams rather than trying to create new cryptographic methodologies.
Trojan proxies shine in evading tight, high-handed censorships in states like China, Iran, and North Korea that employ sophisticated DPI methods against common proxies and VPNs. Blending unobtrusively as regular HTTPS data over port 443, Trojan proxies will make it incredibly difficult for governments or ISPs to detect or restrict your connection.
Many companies and educational institutions apply strict rules of filtering and throttle connections, suspected to be proxy-based. However, if you camouflage your traffic with a Trojan proxy, you can stay under the radar without any problems and this makes it an exceptionally valued tool among remote workers and students who depend on open, steady access to work resources and collaboration tools.
As you might already know, public Wi-Fi networks in airports, cafés and hotels are often hot spots for snooping and malware attacks. But, with a Trojan proxy that adds a critical layer of encryption and obfuscation, your banking transactions, confidential emails and passwords will become impossible to be intercepted. So, you can rest assured that your most sensitive data is never at risk, not even for a second.
If you are a journalist, political activist, or whistleblower, you must know that you need to have an untraceable and secure connection. And this is where Trojan proxies come into your help by camouflaging all of your communications to look like ordinary HTTPS traffic and make them undetectable even by the most intrusive surveillance systems.
Since a Trojan proxy operates on port 443 and appears just like regular HTTPS traffic, it slip with ease past most governmental, corporate, or school firewalls that normally block commonly used proxy ports.
Network administrators or monitoring tools will see nothing unusual since your traffic behaves and looks exactly like regular HTTPS data. So, if you are in an environment where the usage of proxies is closely monitored, you will have a huge advantage with a Trojan proxy.
All non-Trojan traffic is routed to a fully functional website, which means for any authentication attempt that fails, it will simply be routed as regular web traffic. So, you won't raise any suspicion alarm and you'll have continuous access in any of your online activities.
Although there is a brief delay during the TLS handshake, your browsing speed after authentication is generally similar to the performance of a SOCKS5 proxy. So, even if you stream, have large downloads or have a night gaming session, Trojan proxies won't let you down.
Given the performance and services we provide we can proudly say that our prices are very small and fair. Check out our pricing page and we promise you won't be disappointed.
We're offering more than 100 locations for our proxies and we constantly refresh our list to add more locations from all over the world.
Sometimes the kind of support you offer means more than your product and we know that. We're always available and you can give us a try.
Underperforming IPs are detected and replaced automatically. You don't need to manage health manually.
Our proxies are hosted on enterprise-grade datacenter hardware. Expect sub-100ms response times for most targets with no bandwidth throttling.
All our VPN are offered with dedicated IP addresses. As opposed to other providers, we do not rotate and recycle IP addresses
Our Amnezia VPN servers are always kept to the latest version ensuring maximum privacy and alignment with the official packages.
Each month you can replace your proxies without our intervention. Our control-panel allows you to achieve such advanced operations.
We don't sell you packages. You can pick each IP address individually by subnet, city, state or country. You're in full control.
All our servers are attached to 1Gbps and 10Gbps connections and we constantly update our networking stacks to maintain a top position in terms of speed.
Our proxies are activated instantly once your payment enters our system and we really stand behind this word which is not just for marketing.
Our automation suite constantly monitors and checks the proxies against IP leaks or DNS leaks to ensure elite anonymity for our customers.
We're not placing any sorts of limits on your bandwith so you can enjoy really fast and responsive proxies for your applications.
From status checkers to supervisors and service testers we have it all. Our stack is fully automated and self-healing without any intervention.
Don't want to use a username and password combo to authenticate to your proxies? No problem, you can use your ip address instead.
All our proxies are carefully set and monitored in order to ensure they are 100% anonymous and without any sort of ip or dns leaks.